AI-Powered Mobile Application Security Analysis System

🚀 Introduction
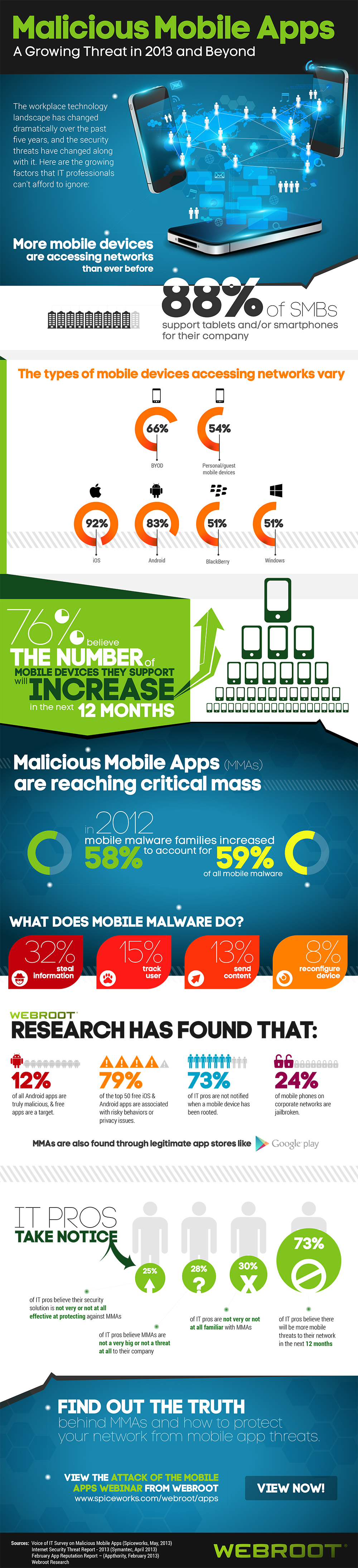
With the rapid growth of mobile applications, security has become a critical concern for developers, organizations, and users. Millions of apps are deployed every year, and many contain vulnerabilities that can be exploited by attackers.
To address this challenge, I developed the AI-Powered Mobile Application Security Analysis System — an intelligent platform designed to automate the detection and analysis of security vulnerabilities in mobile applications using advanced AI techniques.
🎯 Project Overview
This project is focused on building a smart cybersecurity system that combines:
- Artificial Intelligence 🤖
- Static & Dynamic Analysis 🔍
- Vulnerability Detection ⚠️
- Automated Reporting 📊
The goal is to reduce manual effort in security testing and provide fast, accurate, and scalable mobile app security analysis.
Modern research also shows that automated systems are essential because manual testing cannot keep up with the increasing number of applications and evolving threats.
🧠 Key Features
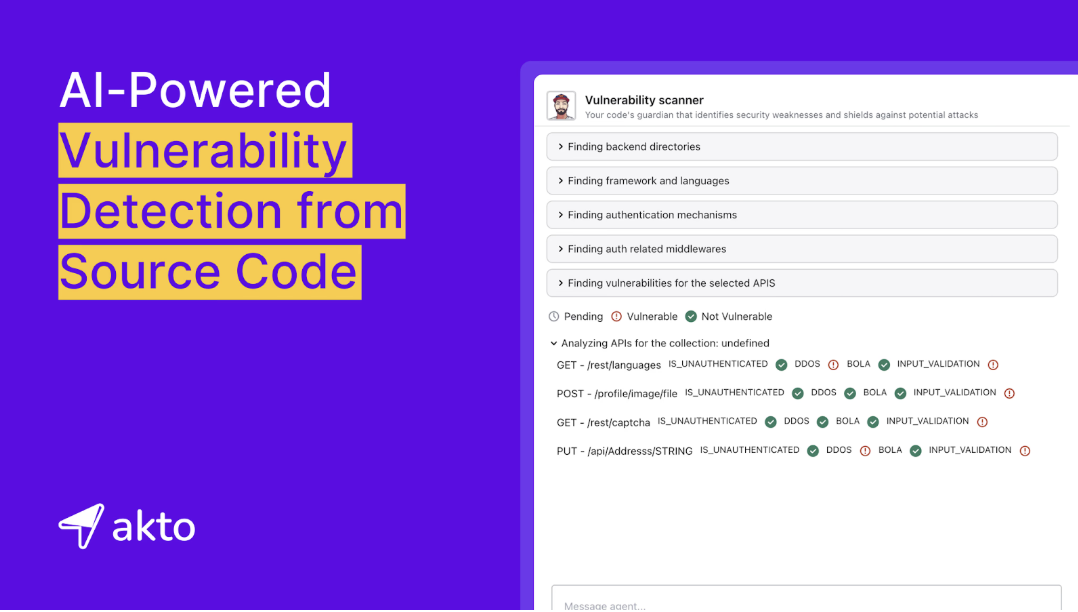
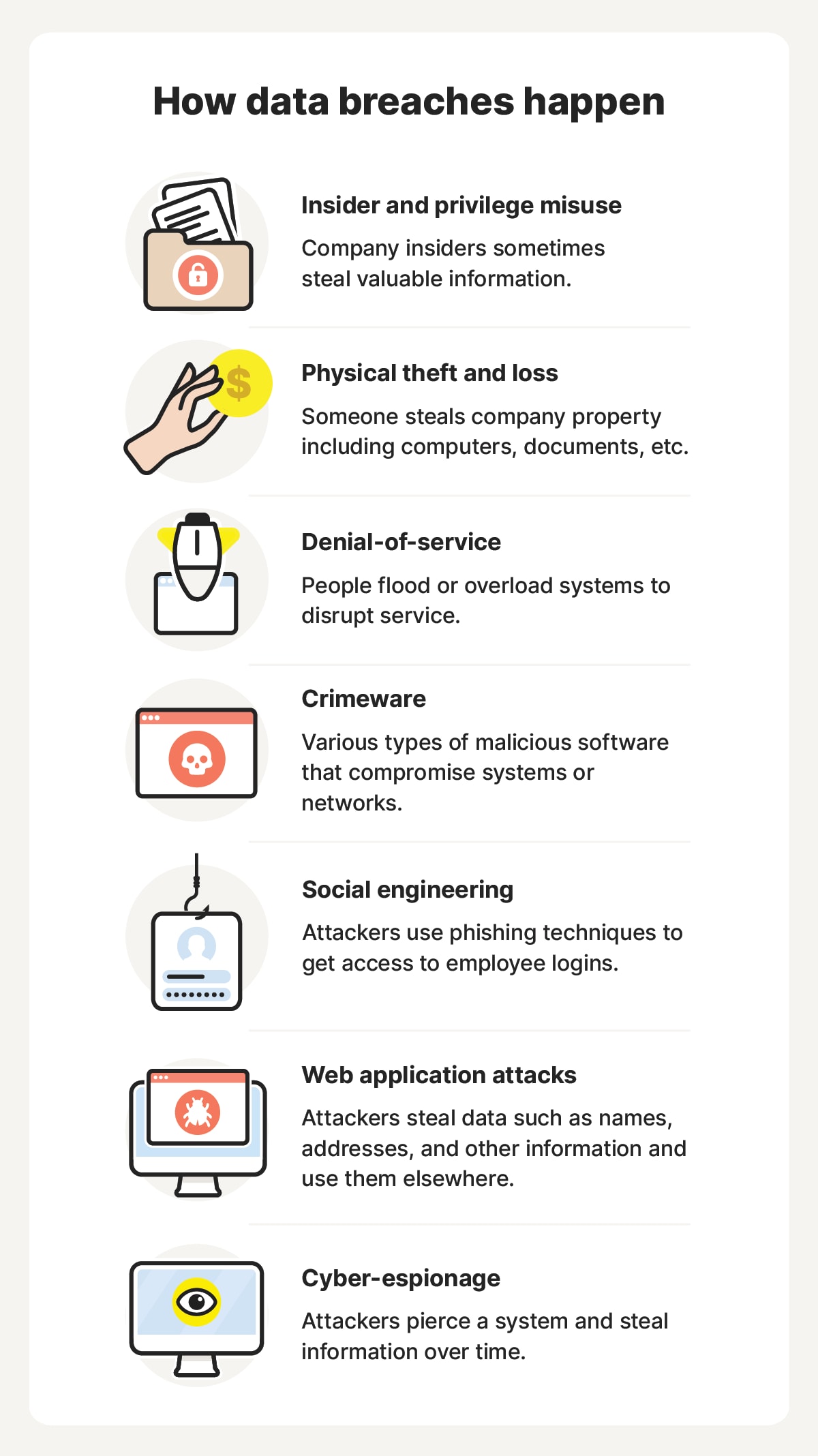
🔹 1. AI-Based Vulnerability Detection
- Uses intelligent algorithms to detect hidden security flaws
- Identifies patterns similar to known malware behaviors
- Improves detection accuracy over time
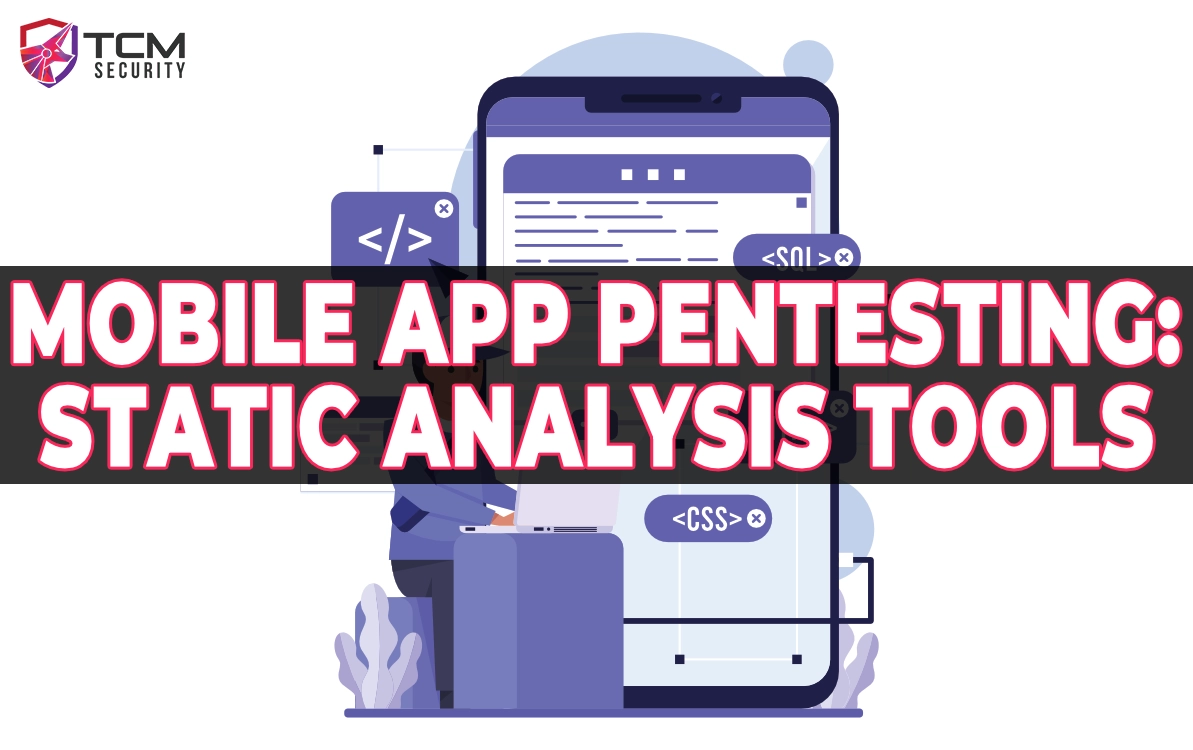
🔹 2. Static Code Analysis
- Analyzes application source code without execution
- Detects:
- Hardcoded credentials
- Insecure APIs
- Weak encryption
🔹 3. Dynamic Analysis
- Runs apps in a controlled environment (sandbox)
- Monitors runtime behavior
- Detects malicious activity such as:
- Data leakage
- Unauthorized access
🔹 4. Automated Reporting System
- Generates detailed security reports
- Highlights risk levels (Low, Medium, High)
- Provides actionable recommendations
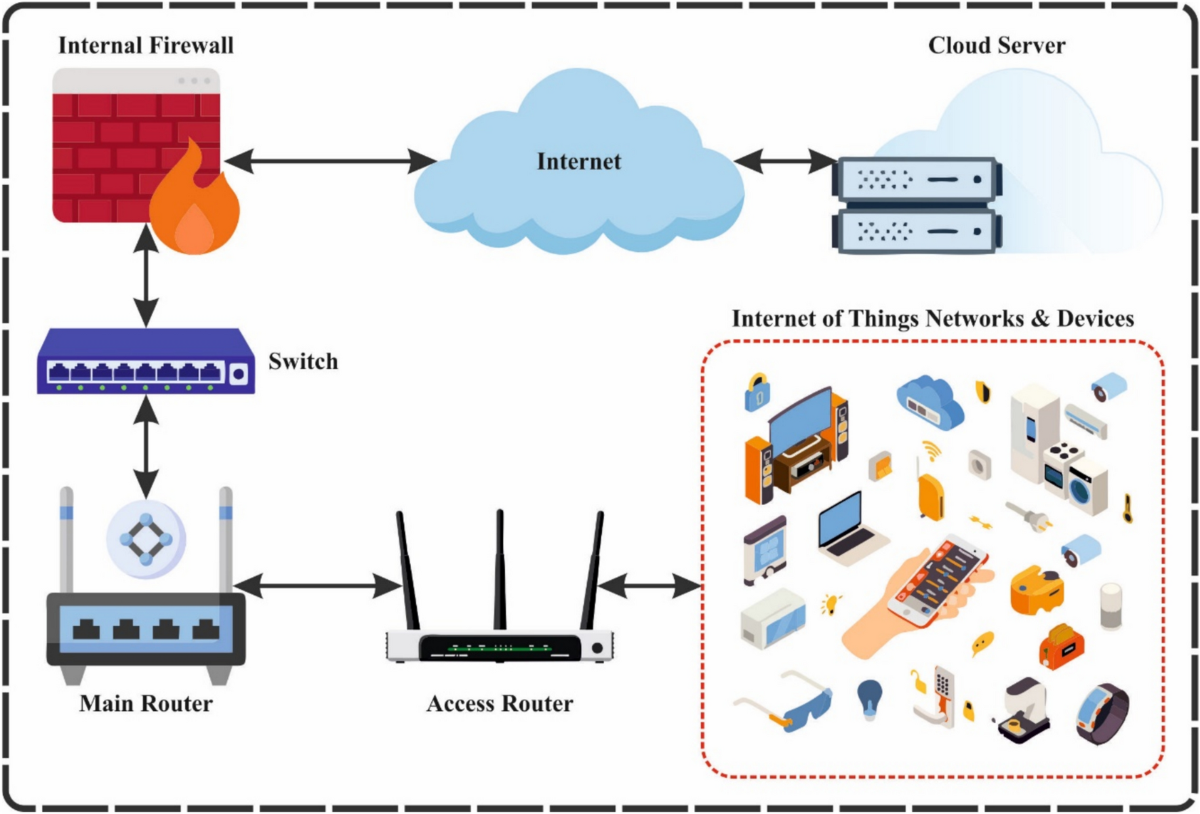
⚙️ System Architecture
The system is designed using a modular architecture:
- Input Layer
- Upload mobile application (APK or source code)
- Analysis Engine
- Static Analysis Module
- Dynamic Analysis Module
- AI Detection Engine
- Processing Layer
- Data extraction
- Pattern recognition
- Risk evaluation
- Output Layer
- Security report
- Visualization dashboard
🔍 How It Works
- Upload the mobile application
- The system scans the app using static analysis
- The app is executed in a sandbox for dynamic monitoring
- AI models analyze behavior and detect anomalies
- A detailed report is generated with findings
🛠️ Technologies Used
- Python – Core backend logic
- Machine Learning / AI Models – Threat detection
- Android Analysis Tools – APK inspection
- Cybersecurity Frameworks – Vulnerability scanning
- Data Visualization Tools – Reporting dashboard
📊 Real-World Impact
This system can be used by:
- 🔐 Cybersecurity professionals
- 🏢 Software companies
- 📱 Mobile app developers
- 🎓 Researchers
It helps in:
- Detecting vulnerabilities early
- Reducing security risks
- Improving application reliability
- Saving time and cost in manual testing
💡 Why This Project Matters
Mobile devices are a major target for cyberattacks. Traditional tools often fail to detect advanced or unknown threats.
This project introduces:
- Automation → Faster analysis
- AI Intelligence → Smarter detection
- Scalability → Suitable for large-scale environments
Research in mobile malware analysis highlights the need for automated systems capable of analyzing large datasets efficiently and identifying new threats.
🔗 GitHub Repository
👉 Explore the full project here:
https://github.com/mianumairusa/AI-Powered-Mobile-Application-Security-Analysis-System
📈 Future Improvements
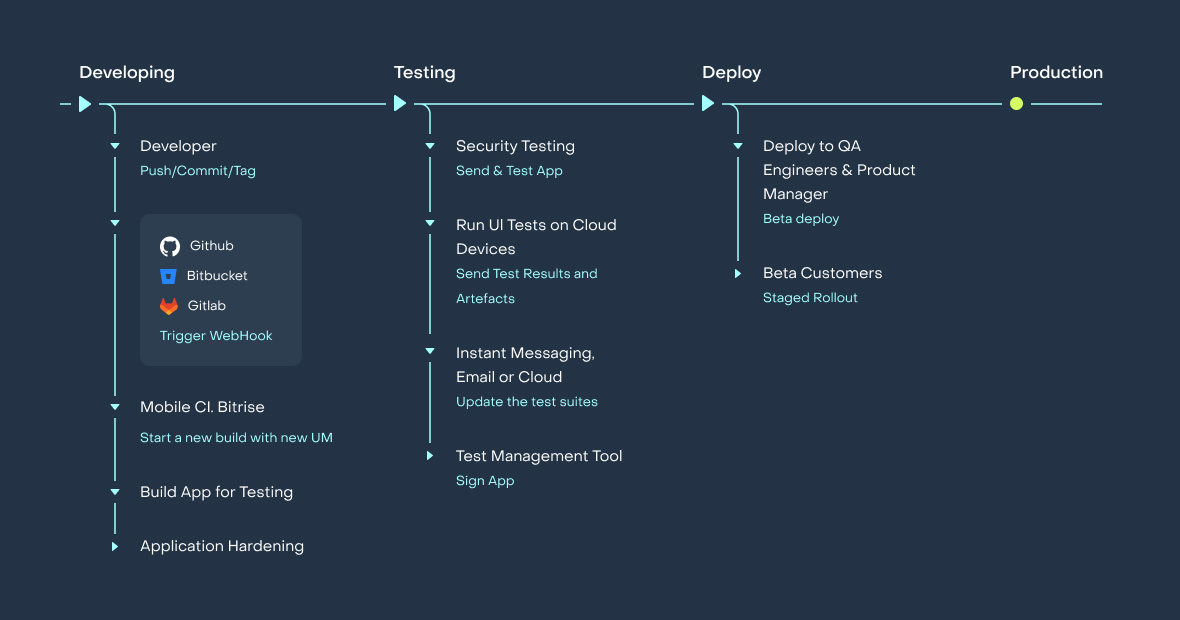
- Integration with cloud-based security platforms ☁️
- Real-time threat detection ⚡
- Advanced deep learning models 🧠
- Support for iOS applications 📱
- API-based integration with CI/CD pipelines 🔄
👨💻 About the Author
Muhammad Umair Shahid
Cloud Security Engineer | AWS Security | Cybersecurity Specialist | Ethical Hacker | DevSecOps | AI Security Researcher
I specialize in building intelligent cybersecurity solutions that combine Artificial Intelligence with real-world security challenges. My work focuses on developing scalable systems that enhance digital protection and automate complex security processes.











Very Useful Information & Project
Thank you for sharing