🚀 Introduction With the rapid growth of mobile applications, security has become a critical concern for developers, organizations, and users….
Muhammad Umair Shahid
Cloud Security Engineering (AWS)
Penetration Testing
Security Monitoring
Risk Assessment & Mitigation
Sensitive Data Protection
Muhammad Umair Shahid
Cloud Security Engineering (AWS)
Penetration Testing
Security Monitoring
Risk Assessment & Mitigation
Sensitive Data Protection
Blog
April 4, 2026
Why Every Hacker Needs to Understand Kerberos Attacks
A Quick Thank You Before diving in, a huge thanks to the offensive security community — from the creators of…
April 4, 2026
VoIP on Zyxel switch
In today’s networks, Voice over IP (VoIP) has become a core communication service for both businesses and labs. To ensure call quality…
April 4, 2026
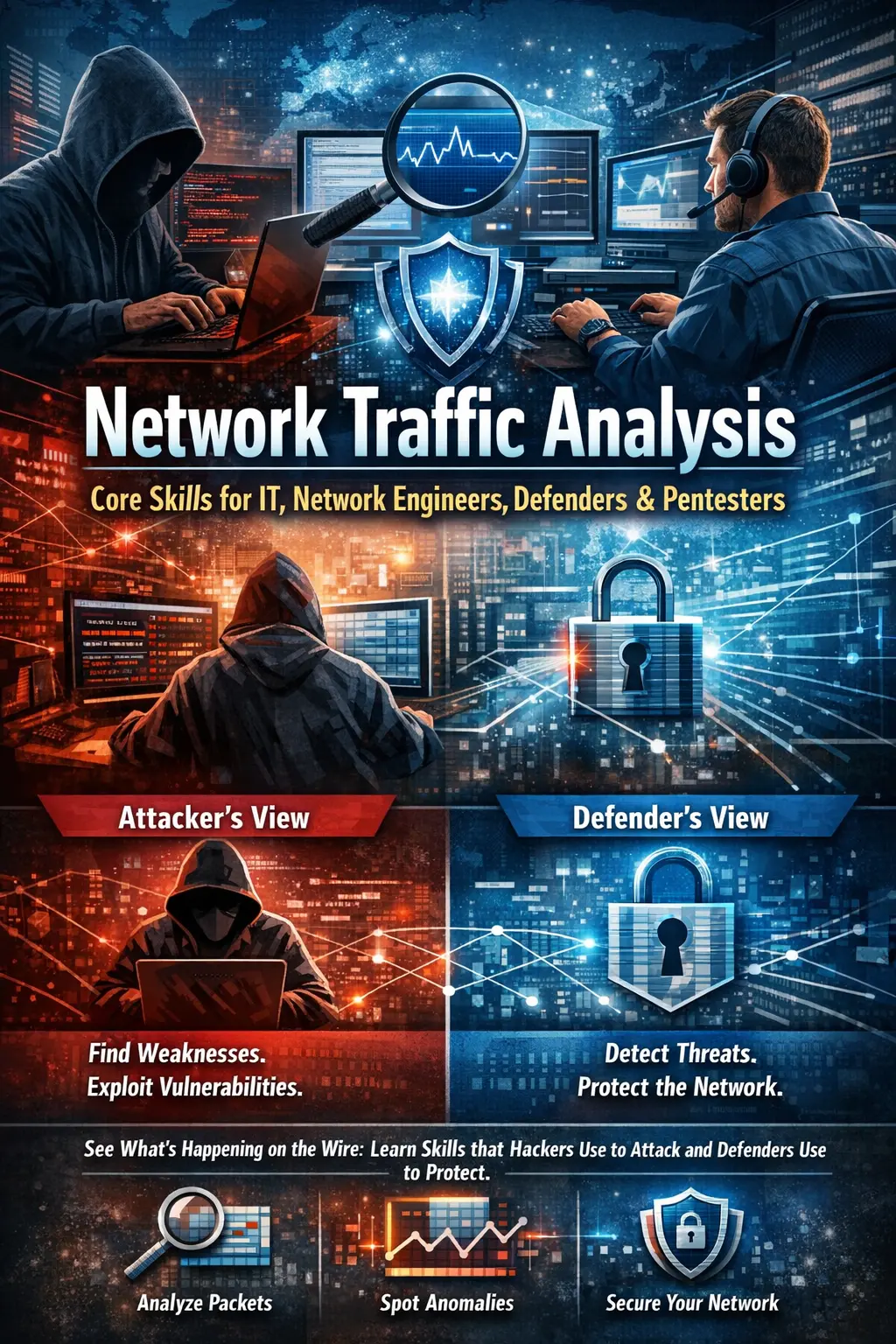
Network Traffic Analysis
Introduction Every system tells a story. Not in logs. Not in dashboards. But on the wire. Every login, every file…